User Access: Orgs, Domains, & Roles
How B2B users are configured in UE Auth
Accounts
Accounts in UE Auth represent users or persons that access systems and products. They are a unique pool of such users specific to your platform instance (AuthGroup) and all have unique identification through an email address and a user ID.
Accounts are Unique
No two users can share an email address or an Account ID (user ID).
From a billing perspective, United Effects considers any account that is not blocked and active (defined as the active property set to true) to be a billable user within one of the pricing tiers.
Additionally, there are two classifications of a user Account, B2C and B2B. All Accounts begin as B2C.
An Account is considered as B2B if any of the following are true:
- The Account has been attributed to an Organization
- The Account has MFA enabled
- The Account has an associated Organization Profile
If an account does not have one of the above properties, it is considered B2C.
Accounts can be B2C or B2B
United Effects bills based on active, non-blocked users. B2C users are billed at a lower rate than B2B.
All Users
To view all users within your platform, open the Users window using the Start button.
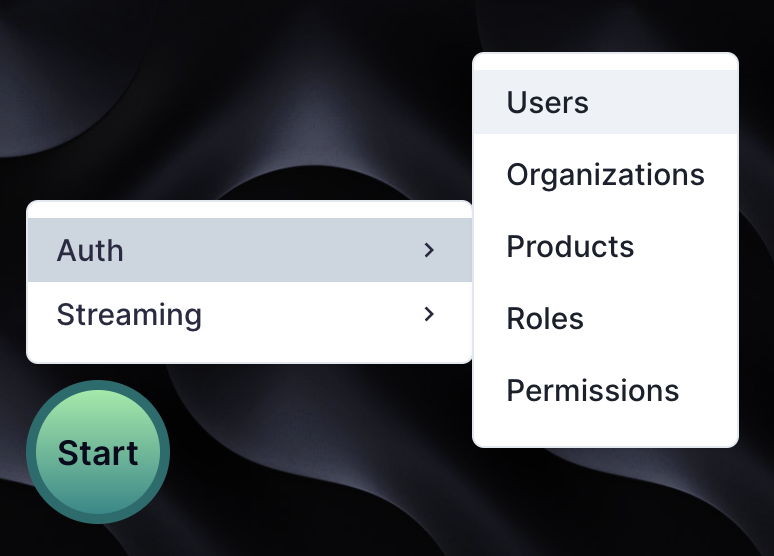
You will be presented with a new window in the experience that shows all Users. To browser users regardless of organizations they may be assigned, click "All Users" on the left nav of this window.
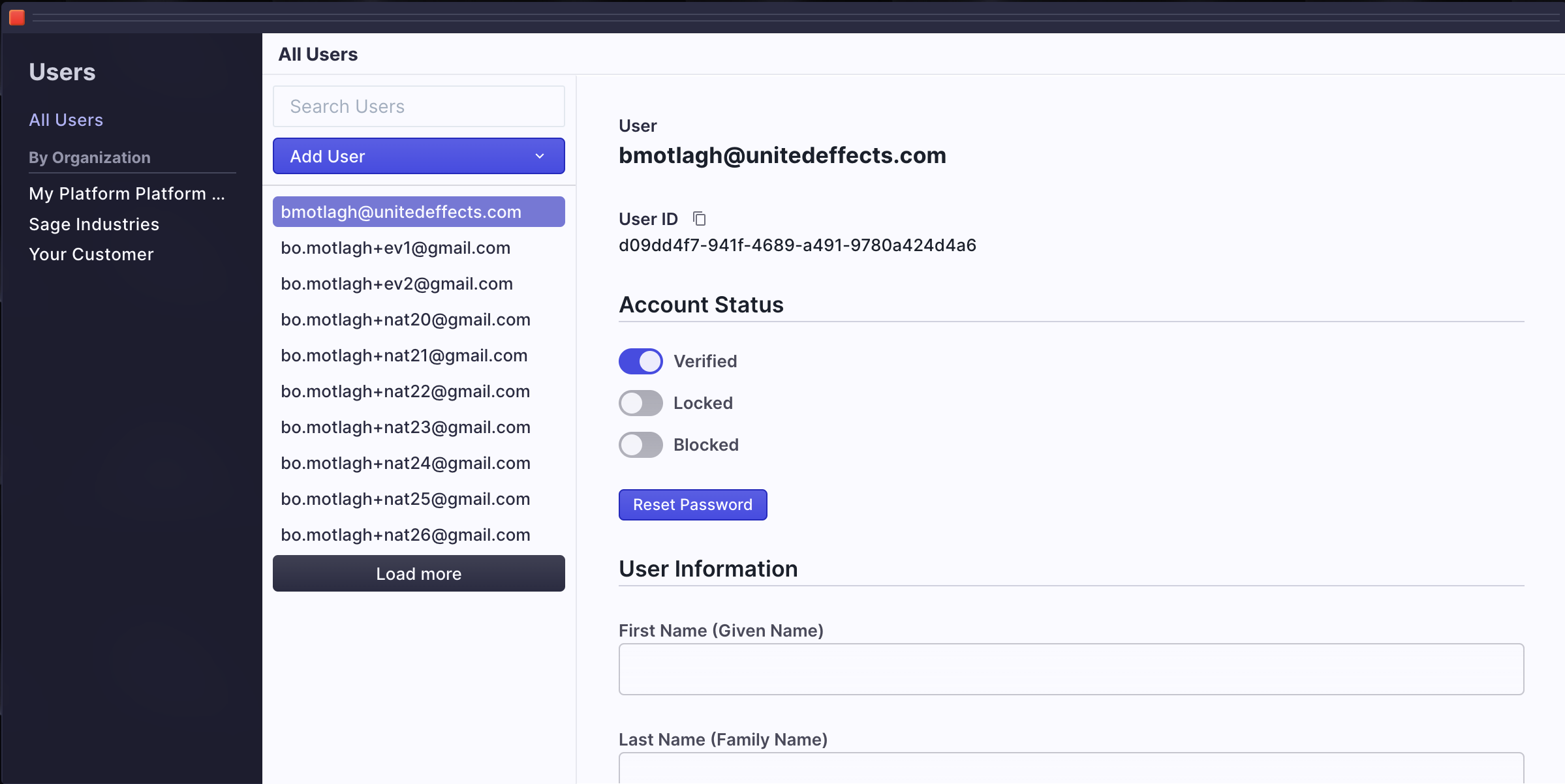
In this example, my Account is highlighted. You'll notice that there are several properties visible.
- My email address is at the top of the details page
- My unique user ID is available and can be copied
- My account is verified and shown as such with a toggle. As an admin, I can manually verify or disable verification for a user. I can also send a request that they self verify.
- If a user or an admin ever feels that the account has been compromised, they can "Lock" that account. This is a temporary measure that can be undone by an admin or by the user themself if they have previously generated lock codes.
- Blocked users are prohibited from authenticating and there is nothing they can do to change that status until an admin decides to unblock them. Blocked users are not billable.
- There is a button to request that the user reset their password. Clicking it will result in an email notification to the user.
Locked vs. Blocked
Locked users can restore their own access using their emergency codes. Blocked users cannot restore access without help.
In addition to these properties, you'll notice that there is a User Information section. This data is a reflection of my Secure Profile, and is only visible because I am the logged in user. Even admins cannot directly access a secure profile without permission. If I were to click a different user where I do not have permission to view their secure profile, I am presented with a button to request access.
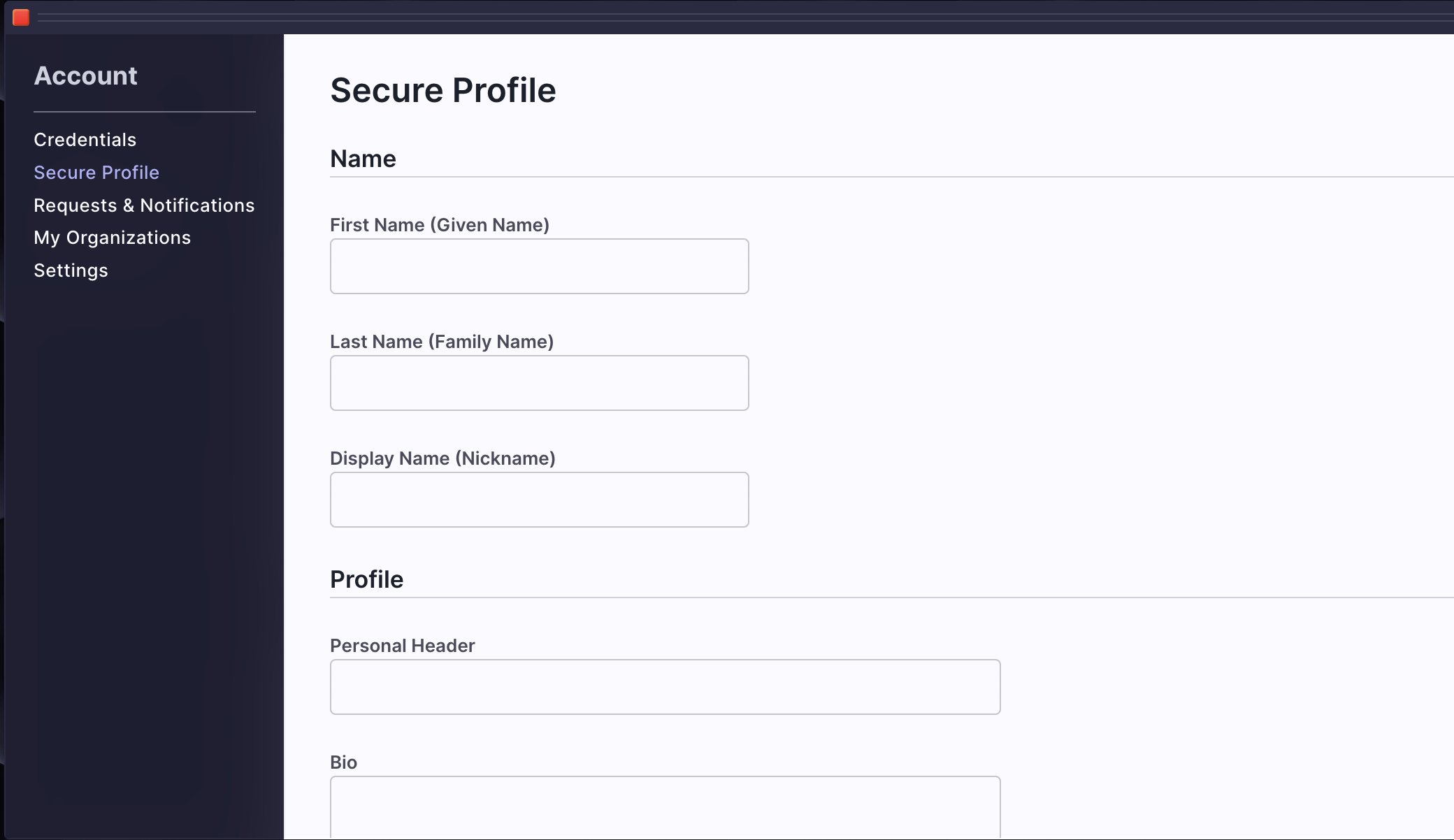
Secure Profile Overview
United Effects values data privacy as the primary concern for all accounts. To help ensure this data is secure, we have built the concept of a Secure Profile. Unlike other identity management solutions, UE Auth does not allow profile data to be shared as part of a login flow through scopes. Instead, we require that the data be managed by the user themself and all access to be requested and approved.
There are two ways for a secure profile to be initialized.
- During user creation (see further down), as an admin creating a new account, you are able to specify a first name and last name for the user. This will initialize the secure profile.
- If the user opens up their account dashboard window and adds data to the secure profile page.
There are 3 ways to request access to a secure profile which are all defined in our API.
- Direct access request for a time. This sends a notification via email or MFA app to the user and lets them approve or deny the request. If approved, the requesting party is given temporary permission to directly query the user's profile via API calls.
- Copy requests will send the data of a secure profile to an outside party or web service as a callback. This request can be useful for automated flows where upon approval, an external system needs to make a copy of the data.
- Syncing requests will copy the secure profile data to the organization profile (see further down).
We Recommend B2B Flows Leverage Organization Profiles, not Secure Profiles
In general, if you are building a secure B2B access model and you wish to include personal information about employees or users, you should likely be using Organization Profiles and not Secure Profiles.
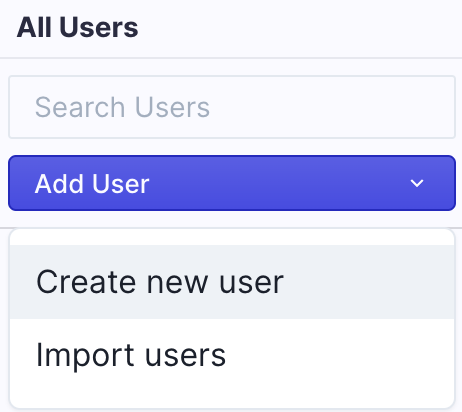
User Creation
You can create users individually or import them in bulk from this view as well.
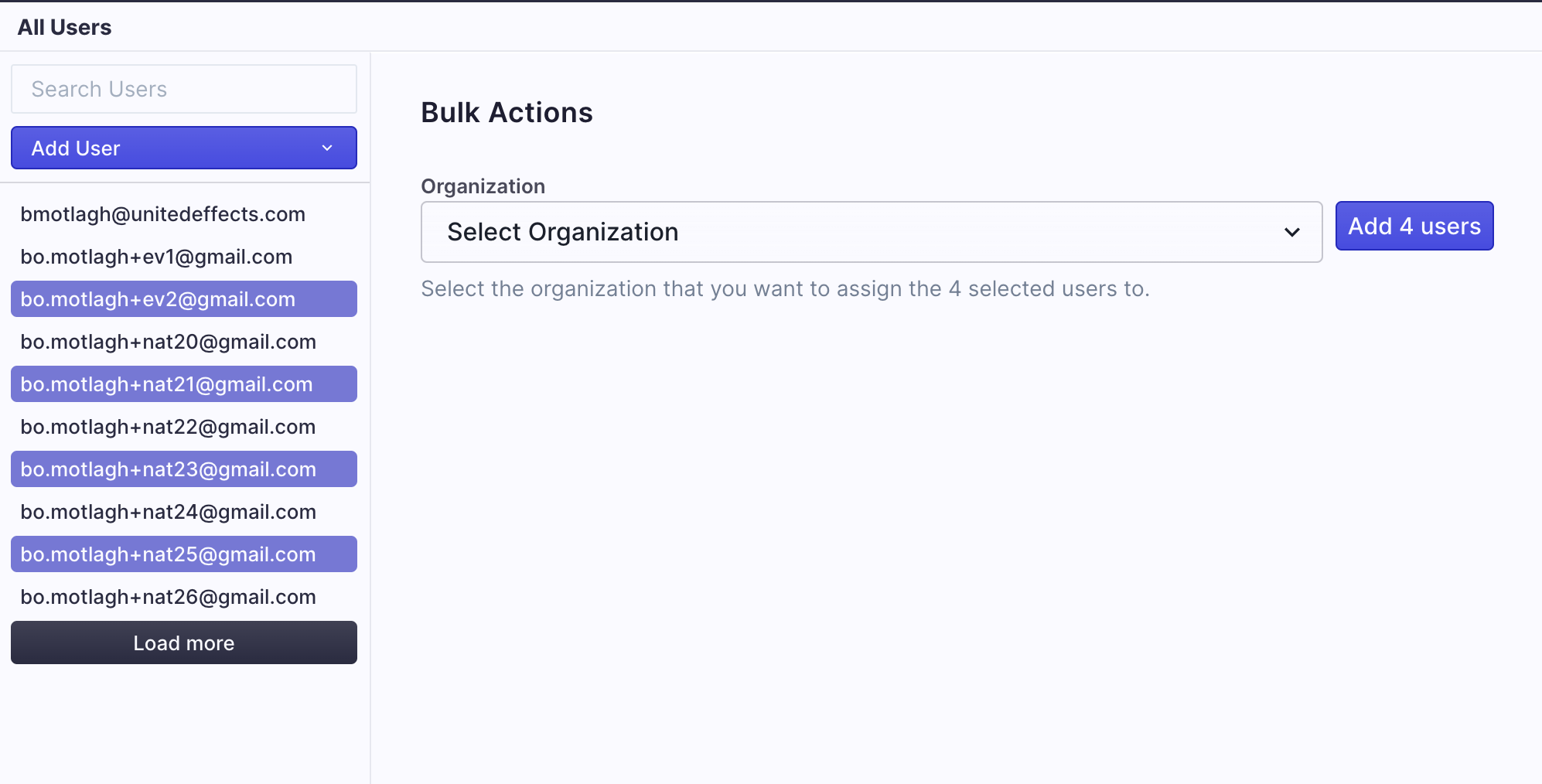
Bulk Organization Assignment
To add multiple users to an organization, simply highlight the ones you wish to assign and use the resulting window.
Organizations
Once assigned to an organization, all users within that organization can be viewed simply by highlight that org on the left nav. In the example below, we've highlighted "Sage Industries", a fictional example of a customer company.
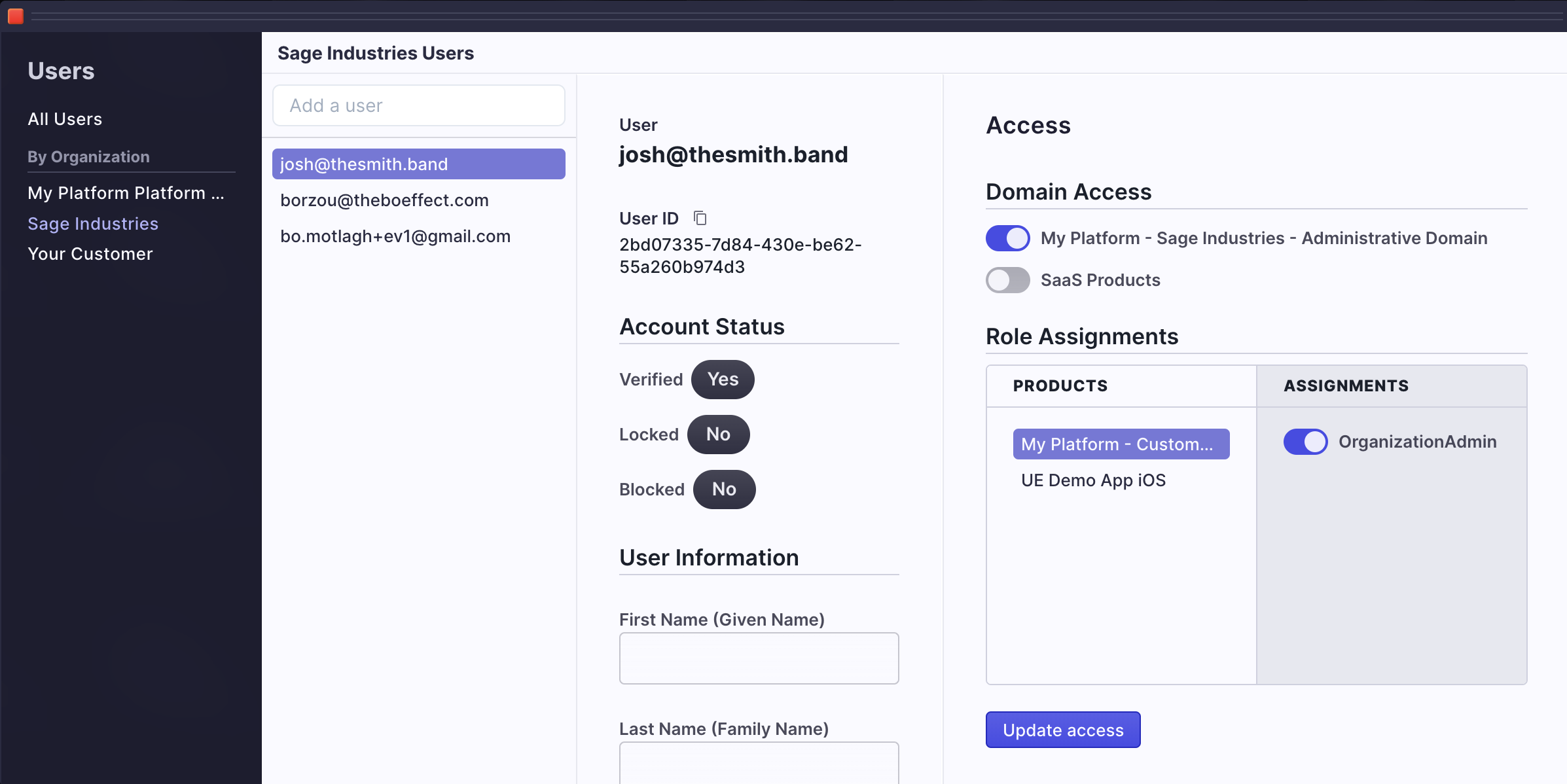
You'll notice that the resulting view is similar to the "All Users" view but with no access to actually alter the user's account status. This view is designed for organization admins, those users who may belong to Sage Industries and are in charge of administering their own users.
In fact, any user that has been given administrative access to manage an organization can add other users to that organization, assuming the organization allows the email domains of the users being added (see restriction options here).
In the above picture, user with email "[email protected]" is defined as an organization admin by virtue of his domain, product, and role assignments which you can see on the right of the window. Every organization has an "Administrative Domain", a "Customer Portal Product", and an "OrganizationAdmin" role. You can assign any users to this role in any organization.
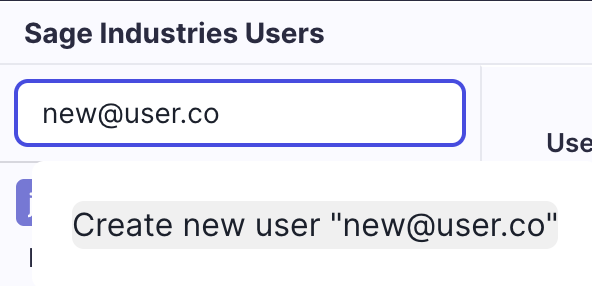
As an admin (platform or organization) you can add users by searching for them in the pool of existing users or by creating new ones using the "Add a user" input field.
Organization Profile
You may have noticed that this view of the user also includes user information. This is not the same as the user information under All Users. When under the context of an organization, user data is the "Organization Profile" data. When under the context of all users, it is the "Secure Profile" data.
The Organization Profile data allows an organization to map data about the user that is separate and distinct from that of the user's personal secure profile data. It is possible that this data might be the same data that the user would define in the secure profile, but ultimately that is the user's decision and not something that is enforced by the system. The point of an organization profile is so that orgs can map employee or resource data about the people they are assigning product access.
| Organization Profile | Secure Profile |
|---|---|
| Can be viewed by any users with appropriate permissions to the organization. | Can only be viewed by the Account holder and by those for whom they approve access on a temporary basis. |
| Can exist without the permission of the associated Account. | Can only exist if initialized during user creation or by the Account holder directly. |
| Can be synced with the secure profile upon request only if the Account holder approves. | Can never be copied or accessed without explicit approval by the Account holder. |
| Can be updated by the organization as desired for their internal data management. This includes the associated Account's name, biographic data, and other information. The Account holder has no access to alter this data, it is owned by the organization. | Can only ever be updated by the Account holder. The user should be careful when allowing access requests of type "Copy" because the resulting external source is the profile is copied to is beyond their control. |
In addition, the following are important features of the Organization Profile.
- While associated account holders have no power to alter or delete an organization profile, they are always kept informed of the existence of one even if the user account is no longer associated to the organization.
- Account holders are provided with the ability to request Organization Profiles be deleted, though they cannot enforce compliance with this request. When a user makes such a request through the UI or API, an email notification is sent to the organization primary email as defined by that organization's administration data.
Organization Profiles are for B2B Resources
The point of an organization profile is so that organizations can map employee or resource data about the people they are assigning product access while still respecting the person's personal data security.
Access
On the right side of the organization user window, you can see the access features of UE Auth. This is where you can assign a B2B user access to a specific product, roles, and finally permissions through those roles if they've been assigned. In other words, this is how you can learn exactly what an authenticated user should be allowed to do once logged into your systems.
Domains determine product access. If you recall from our article on setting up organizations and domains, the licensed products of an organization are further assigned to domains so that you can define access to some but not all products through these groupings.
Within the context of a domain, the available products of that domain are then listed. You can select whichever products you are granting access to the user. Currently, product access is an AND operation that works globally for the user. If the user has access to domain 1 with product A and domain 2 with product B, then the users' access is communicated as an aggregate of product A and B. It is up to the enforcement system of the products to determine further refinement if desired.
Product Access is an AND Operation
If the user has access to domain 1 with product A and domain 2 with product B, then the users' access is communicated as an aggregate of product A and B.
Lastly, within the context of a product, there are roles that can be assigned to the user. Roles may or may not have permissions associated to them. If they do, all permissions associated to the role are then assigned to the user as well. For a deep dive into how UE Auth Permissions are structured and work, click here.
Once you've toggled all the necassary access, you can simply click "Update Access" to assign the changes. The user will receive an email notification that their have new permissions and organizational access.
Updated over 1 year ago